Internationally, the expeditious adoption of digital technologies is facilitating advanced and disruptive business models and processes across organizations of all sizes and industries.
This; however, makes products and processes vulnerable to cyberattacks, with the risk expanding with each connected application.
Many organizations have recognized cybersecurity as a major organizational risk to their strategic goals and initiated different programs to analyze and manage those risks. Despite these increasing expenditures in cybersecurity, organizations are still subject to security and data breaches.
According to the Global Cybersecurity Outlook INSIGHT REPORT released by the World Economic Forum in January 2022, the cost of breaches to an organization is high, amounting to an average of US$ 3.6 million per incident.
Perhaps even more troubling is the growing trend where companies need 280 days on average to identify and respond to a cyberattack. To put this in perspective, an incident that occurs on January 1 may not be fully contained until October 8.
Security breaches observed in the past suggest that decision-makers were, in many cases, either unaware of security threats or ignored advanced warnings from their security specialists.
Given their lack of strategic view on cybersecurity risks, or simply their lack of proactive preparation, these organizations have to resolve the problems that have arisen after a successful cyber-attack.
Cybersecurity and risk management leaders are faced with an array of information security frameworks, control catalogues, and processes, all intended to inform the design of their security programs.
While Gartner assumes that through 2024, ISO 27001, the National Institute of Standards and Technology (NIST), and Cybersecurity Framework (CSF) will remain the predominant enterprise security frameworks complemented by localized and industry- specific standards and regulations.
There is always a need for each organization to develop a strategy to critically understand its DNA to be able to effectively and efficiently adopt the ISO 27001 and NIST concepts, best practices, controls, or even recommendations.
Most organizations, especially large ones, tend to develop their mechanisms or systems to analyze the interrelated organizational components such as objectives, processes, roles, responsibilities and even their events and triggers.
But most of the time, those types of analysis are oriented towards its digital transformation activities and to achieve new or enhanced business capabilities.
The more those organizations capitalize on the enterprise architecture concepts, and institutionalize them in their daily operations, the more they achieve business capabilities, new businesses, more profitable models, and new revenue streams.
While analyzing the success stories of the organizations that managed to capitalize on enterprise architecture practices to successfully transform their business, it is obvious that the most successful organizations are those who managed to adopt a multipronged approach.
First, link the Enterprise architecture activities to the business strategy, adopt a business-outcome- driven enterprise architecture approach, prioritize business architecture, and then link IT efforts to business direction and strategy.
Second, avoid restricting the EA team to the IT organization and manage to build a robust enterprise architecture team that consists of a core, virtual, and fusion team resources from across the organization.
Third, avoid pursuing the enterprise architecture program with the lack of pre-developed key performance metrics, construct an initial set of enterprise architecture practice efficiency metrics, and soon after, construct a set of enterprise architecture practice effectiveness metrics.
Fourth, demonstrate the business value of enterprise architecture to business leaders by targeting EA efforts to deliver “just enough” and “just in time.”
Fifth, avoid viewing EA as a finite process and manage to treat EA as a continuous and iterative effort offered as an evolving portfolio of services designed to meet stakeholder needs.
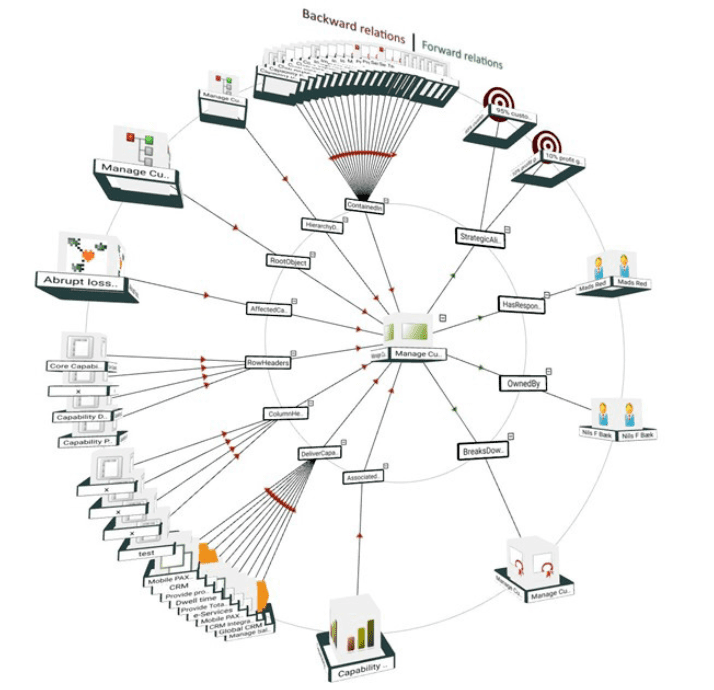
3D visualization of an object in QualiWare X
Government organizations are under huge pressure to transform their services to sustain and grow the citizen services and to elevate their digital business and citizen index.
Private organizations need to transform to build and grow their business capabilities.
The enterprise architecture was and still is the right tool to boost these efforts that protect organizations from digital transformation activities (which are innovation activities focused on disruption initiated by their competitors).
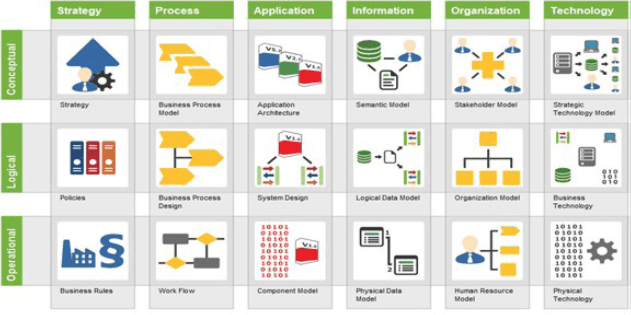
QualiWare Enterprise Architecture Framework
Cybersecurity and risk management leaders also need the right tool to understand the organizational DNA in a way that is integrated and connected, but at the same time, loosely coupled enough to allow them to identify hundreds or thousands of different attack scenarios, enforcing the business modelling languages as a way to communicate the business cybersecurity risks.
The depth of adoption will enable organizations to capitalize on new spaces that become available using AI capabilities.
Enterprise Architecture as a tool (a way of thinking and not technology) will help cybersecurity leaders to build the right framework to protect the organization from innovative hacking or attacking activities focused on disrupting the business.
Adopting the enterprise architecture concepts to understand the business artifacts (objectives, roles and responsibilities, processes, things and technologies, locations and events and triggers), model them, analyze them, and design them, will help organizations build the right cybersecurity framework that perfectly fit their specific needs, “Just Enough”,and “Just in Time.”
Compared to the success achieved by the organizations that adopted the enterprise architecture for digital transformation, the security architects need to:
- First, link the cybersecurity to the business objectives
- Second, build the cybersecurity key risk indicators and link them to the organizational key performance indicators,
- Third, avoid restricting the cybersecurity responsibilities, accountabilities, knowledge and experience to the technology leaders, and to stop throwing money on problems by investing only in technology since most of the cyberattacks are successful because of the lack of proper cybersecurity processes and or people awareness, and
- Fourth, avoid viewing cybersecurity as a finite process.
The last-mentioned aspect might be the most critical considering that most internationally recognized cybersecurity frameworks are control based, and eventually become a compliance framework where organizations get used to following the controls as a check list.
Eventually, this leads to the Boiling Frog Syndrome, (although it is not proven) that the Frog boiled to death as it was adapting to the tiny disruptive changes.